

A SOC is not just a technical setup. It is a strategic nerve center where human expertise, intelligence-driven processes, and advanced technology converge. It transforms raw data into actionable insights, enabling organizations to detect threats, respond to incidents, and learn from every attack attempt.
A SOC is a centralized unit responsible for continuous monitoring, detection, and response to cybersecurity threats. Unlike traditional IT security measures that are reactive or sporadic, a SOC operates in real-time to anticipate and neutralize threats before they escalate. It is not merely a technical hub but a strategic center where human expertise, automated intelligence, and well-defined processes converge to protect an organization’s digital assets.
Understanding how a SOC works begins with its primary functions:
The SOC workflow provides a systematic approach to managing cybersecurity incidents. While specific practices may vary, most SOCs follow a multi-stage process that ensures thorough and timely response.
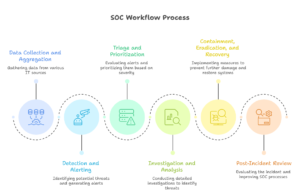
The SOC begins by aggregating data from across the IT environment. This includes logs from servers, applications, firewalls, and endpoints. Centralizing this information allows analysts to detect threats more efficiently and eliminates the inefficiencies of monitoring disparate systems independently.
Automated tools then scan the aggregated data to identify potential threats. Alerts are generated for anomalous activities such as unusual login patterns, data exfiltration attempts, or malware behavior. These alerts form the basis for further investigation.
Not all alerts require immediate action. SOC analysts evaluate each alert to determine its severity and potential impact. High-priority incidents are addressed first, ensuring that critical threats receive timely attention.
Once prioritized, incidents undergo a detailed investigation. Analysts correlate multiple data points, review historical activity, and consult threat intelligence sources. This analytical process enables accurate identification of threats and informs effective mitigation strategies.
After understanding the threat, the SOC initiates containment measures to prevent further damage. This may involve isolating compromised systems, removing malicious software, or applying security patches. Following containment, recovery steps restore affected systems to a secure state while minimizing operational disruption.
The final stage involves evaluating the incident and the response. Lessons learned are documented and fed back into SOC processes. Post-incident reviews help improve detection rules, refine workflows, and strengthen the overall security posture.
A SOC’s effectiveness depends on the seamless integration of people, processes, and technology.
At Sattrix, running a SOC is more than watching screens. We create intelligent command centers where automation, real-time monitoring, and threat hunting come together to stop problems before they become disasters. Our teams work across the USA, India, MEA, Spain, and Malaysia, which means we track threats from all over the world and act quickly no matter where they appear. We combine human expertise with smart technology so decisions are fast, practical, and effective. With Sattrix, cybersecurity is not just about protection. It is about confidence, keeping businesses running smoothly, and turning security into a clear advantage.
A Security Operations Center is far more than a monitoring facility. It is the strategic core of organizational cybersecurity, combining continuous vigilance, structured workflows, and analytical rigor. By understanding how a SOC works, organizations can appreciate the sophistication of the SOC workflow and process. From data collection to post-incident review, each stage is designed to anticipate, detect, and neutralize threats before they compromise critical assets.
In a world where cyber risks are constant and evolving, a SOC is not just a tool but a strategic imperative. Organizations that invest in a robust SOC gain resilience, intelligence, and the ability to respond proactively to an increasingly complex threat environment.
A SOC is a Security Operations Center where experts monitor, detect, and respond to cyber threats in real time.
It collects data from networks and systems, detects unusual activity, investigates incidents, and responds quickly to stop threats.
A SOC follows a process: collect data, detect alerts, triage and investigate, contain and fix issues, then review and improve.
Threats can happen anytime. A SOC helps businesses stay ahead, minimize damage, and keep operations running safely.
Sattrix combines human expertise, smart technology, and global coverage in USA, India, MEA, Spain, and Malaysia to act fast and provide proactive protection.